Local Administrator Protection in Windows 11: Getting to Know Its Features
The article content
- What is the local administrator protection option
- How administrative accounts worked before local administrator protection
- What changes have occurred since local administrator protection appeared
- Enabling the local administrator protection function: main methods
- What will happen in the background when local administrator protection is running
- Privilege escalation with local administrator protection
- The role of appinfo.dll in local administrator protection
- Instructions for escalating local administrator protection privileges
- Summing up

The very first version of the Windows operating system appeared in the very distant 1985. Initially, it was just a graphical add-on to DOS, but as an independent product it was launched on the market almost 10 years later, namely in August 1995. In almost 30 years of its work on the market, it has managed to win universal recognition, becoming one of the most popular operating systems around the world. During this period, Windows has undergone a lot of changes and improvements. Among all the versions that appeared on the market, there were very successful ones, as well as those that did not receive enough positive feedback from the user audience. But still, its popularity remains at a very high level.
And so in 2021, Microsoft Corporation presented the next version of the operating system to the world public, namely Windows 11. It implemented many fairly advanced solutions, changes, improvements in comparison with previous versions. Thus, many users noted how serious a step forward was made here in many directions. In particular, a more convenient, thoughtful and functional interface, a lot of advanced features for gamers, improved performance, higher security indicators and deep integration with related applications providing increased convenience and functionality in the work process are noted.
The introduction of advanced technologies — this is what has improved the user experience when working with a computer, increased productivity, and kept personal data under reliable protection. All the improvements that occurred in version 11 of the operating system affected not only ordinary users of home personal computers. System administrators and all those who work with local networks have also noticed significant changes. In particular, we are talking about such a new function as Local Administrator Protection. Its actions are aimed at eliminating permanent administrative privileges, because according to the latest research, they quite often became the most vulnerable spot in the security system and made hacker attacks on local networks successful.
As part of today's review, we will dwell in detail on what the Local Administrator Protection option is in Windows 11, get acquainted with the features of the "shadow accounts". We will talk about how to ensure the protection of local administrator rights. We will tell you how to enable this function and reveal the features of its operation in the background. We will describe the process of increasing privileges step by step. The information provided will help you navigate such an innovation in Windows 11 as Local Administrator Protection, as well as perform all the necessary settings as quickly as possible and without wasting time.
What is the Local Administrator Protection option
Such an innovation in the Windows 11 operating system as Local Administrator Protection is designed to eliminate permanent administrative rights. The traditional solution has now been replaced by the use of a hidden privilege escalation mechanism, within the framework of which the appropriate access rights will be granted immediately as the need arises. That is, elevated rights will not be used until there is an urgent need for them. But all settings will remain active.
You must understand that the presence of local administrator rights on any user device with the Windows operating system in itself opens up unlimited possibilities in accessing any settings. On the one hand, this is quite convenient, as it provides maximum functionality and flexibility in the work process. But on the other hand, the presence of such rights becomes the cause of serious vulnerabilities. The fact is that if attackers manage to gain access to the administrator account, then all devices connected to the local network will be compromised, and important information can be stolen. This is the method most often used by attackers who want to gain control over the system.
For quite a long period of time, a technology called User Account Control (UAC), or split token, was widely used to minimize this risk. This is what allowed tasks with elevated privileges to be launched in a fairly limited administrative field. In practice, such methods have proven to be quite effective, but attackers have learned to bypass them.
The Local Administrator Protection function built into Windows 11 is designed to solve this dependency and significantly improve the security indicators for local administrators. Here, developers have already moved away from the classic use of split tokens, replacing them with a more advanced System Managed Admin Account system (called ShadowAdmin in DLL files). The point is that the account will be created dynamically as the need arises and automatically linked to the main administrative account.
As a result, it will be possible to perform tasks with elevated privileges in a separate context. Thanks to this, access to administrator rights is minimized, which allows you to create a reliable isolated environment. For performing privileged operations. Such a solution can be safely used in practice in many local systems, providing truly high indicators of system security and its resistance to various types of vulnerabilities.
How administrative accounts worked before Local Administrator Protection
Before the Local Administrator Protection function appeared in Windows, the operating system worked as follows when the administrator was connected. Initially, 2 tokens were created:
- Admin token. This implied the presence of full administrative rights. This solution was used in everyday tasks, as an option when opening files, web surfing and allowed to significantly reduce risks.
- Split token. Here, administrative rights were already limited. They were allocated for solving narrow-profile tasks that required high levels of security and anonymity.
But during the installation of programs or making system changes, a UAC pop-up window appeared asking whether the user really wanted to use administrative access rights to solve a particular task. And here the person had to either confirm or deny such an action. If he clicked the "Yes" button, then the program was launched taking into account all the administrator privileges. They remained active until the application was closed.
This approach was intended to ensure sufficiently high security indicators for user devices, in particular, to protect them from accidental launch of malicious software. But the administrator token still remained vulnerable to more complex and sophisticated tasks. Alternatively, the malware remained in standby mode for a certain period of time until the user launched one of the privileged actions, and then hackers could intercept this token and use it for their own purposes.
What changes have occurred since Local Administrator Protection appeared
Since the introduction of the Local Administrator Protection feature in Windows 11, token management has undergone dramatic changes. The system no longer uses the administrator token directly linked to the user account. Windows 11 has now moved the token to a hidden administrator profile, which is under the direct control of the system. In simpler terms, we simply took the administrator's key and locked it in a secure safe until it is really needed. But the code for this safe is only available to the operating system.
Now, if the user needs to perform a task that requires elevated privileges, Windows will not immediately activate the administrator token. Initially, it will switch to a new, managed profile, which is in an isolated environment and uses the token only to solve a specific task. After these tasks are completed, this access is again blocked and again sent to standby mode until the user faces a repeated solution to such a task. That is, even if your system already has malicious software in standby mode, it will not be able to intercept the administrator's token, which is why higher security levels are achieved.
Using a solution such as Local Administrator Protection in practice allows you to minimize the volume of the attacked surface by dynamically creating and linking the System Managed Admin Account and the local administrator in conjunction with increasing privileges if necessary. We would also like to remind you about a solution such as Endpoint Privilege Management (EPM), which uses a virtual account to increase its access privileges. So, in comparison with it, the System Managed Admin Account is already presented as a permanent account that will be stored in the SAM database until it is needed.
Enabling the Local Administrator Protection function: main methods
In order to activate the Local Administrator Protection function on a device with the Windows 11 operating system, you can use one of 2 methods:
- Group Policy, that is, Group Policy.
- Cloud solution for managing endpoints Intune.
Let's consider both options in more detail.
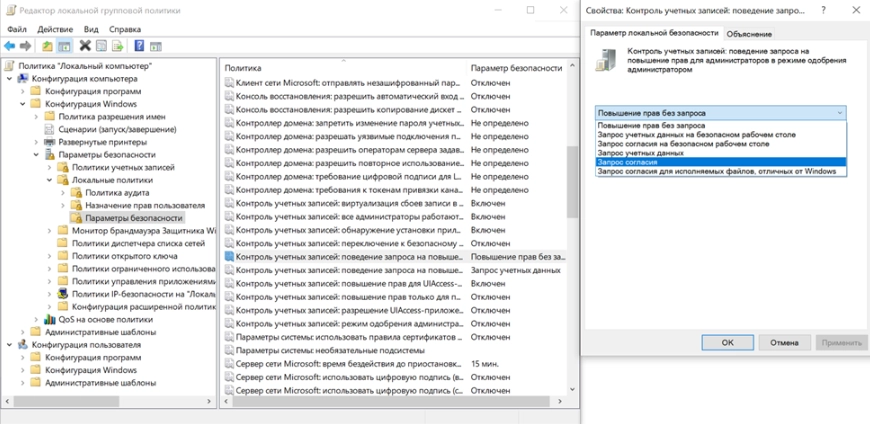
Activating Local Administrator Protection via Group Policy
In order to start Local Administrator Protection via Group Policy, you need to perform a number of simple steps, following our recommendations:
- Run the local administrator protection editor on your device group policy gpedit.msc.
- Here we are interested in such a section as “Computer Configuration”. Next, select the “Windows Configuration” option, and from there go to the “Security Settings” tab. Of all the parameters presented here, we initially select “Local Policies”, and then “Security Settings”.
- Now we configure such a parameter as “User Account Control”. At this stage, you will need to activate the administrator approval mode with administrator protection.

This completes all the settings. In order to finally launch Local Administrator Protection, you will need to reboot your personal computer or laptop.
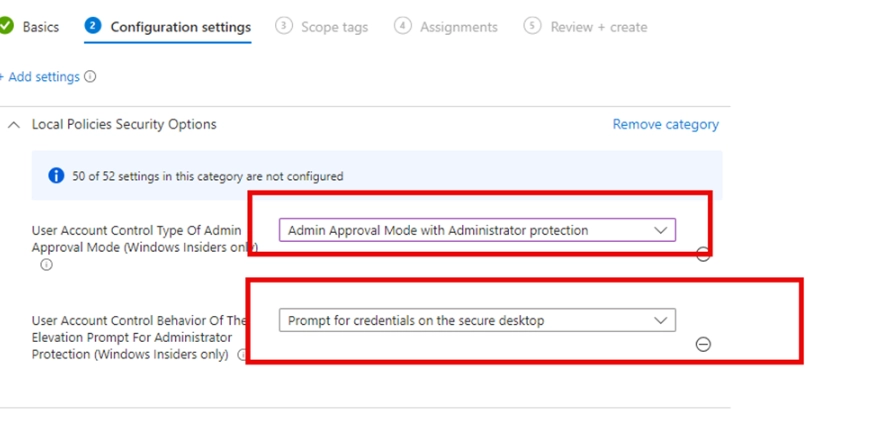
Activating Local Administrator Protection via Intune
Another option to launch Local Administrator Protection on your device is to use the Intune cloud endpoint management solution. To solve this problem, follow our recommendations:
- Log in to the Intune Portal from your device. Here, find the Settings Catalog tab to create your Policy.
- Configuring User Account Control. In this case, we need to activate the administrator approval mode with the presence of extended privilege protection.
- Approve the request to confirm elevated privileges on the secure desktop.

Next, you only need to apply the configured Policy and reboot your personal computer or laptop to finally activate Local Administrator Protection.
What will happen in the background when Local Administrator Protection is running
After you activate the Local Administrator Protection function on your user device, the operating system will dynamically create a separate System Managed Admin Account for each of the local administrators working on your network. To implement this task, a special function samsrv.dll is used, that is, ShadowAdminAccount::CreateShadowAdminAccount. As a result, a new account is created, which is assigned a random name.
It does not matter which option you will use. But it is important to think about your own convenience: you should easily identify individual accounts. Therefore, a universal solution in this case would be to set an account name that would contain the name of your local administrator, such as ADMIN_Ivan, ADMIN_Egor or ADMIN_Ivanov, etc. Thanks to this, you can distribute access rights as easily and simply as possible and avoid confusion.
As a result, you should have separate so-called "shadow" accounts for each administrator working in your local network. The only exception is the account that will be managed by Windows LAPS. Here you just need to follow the rule: the number of accounts is this is the number of system administrators working in your company and one additional account.
After you activate the Local Administrator Protection option and reboot your computer, all subsequent execution of commands on behalf of the administrator will be accompanied by an additional request from the system for confirmation or entry of credentials based on what UAC settings were initially specified by you.
Also, names will be randomly assigned to two specific attributes based on SAM data, in particular:
- ShadowAccountForwardLinkSid. This attribute is formed directly in the registry of the main administrator account of your local network and will link it to each of the new System Managed Admin Accounts driven by you.
- ShadowAccountBackLinkSid. This attribute is created directly in the System Managed Admin Account registry and is intended to ensure interaction between it and the main administrative account.
After you create and bind functions between the main and additional administrator accounts (implement the ShadowAdminAccount::AddAccountToLocalAdministratorsGroup link), the system will automatically add an additional account for each local administrator to the group. If you use the whoami /groups command, you will be able to see how the new System Managed Admin Account will be connected to the local administrators group.
The practical implementation of such integration will indicate that each of the local administrators receives all the necessary rights to perform certain privileged operations. But this eliminates the need to use split tokens.
Privilege Escalation with Local Administrator Protection
We have already mentioned that the Local Administrator Protection function will become available to you after it is activated and your user device is rebooted. Your very first attempt to run the command line directly as an administrator will result in the system sending you an additional request to enter your credentials or to confirm them, depending on what user account control settings you have previously configured.
When escalating privileges with administrator protection activated, you will not see the classic UAC window, typical for all user connections, but a completely updated security window of the Windows 11 operating system. As soon as you confirm the launch or enter your login and password, the command line will automatically open in the context of your System Managed Admin Account.
The role of Appinfo.dll in Local Administrator Protection
Let's start with the fact that Appinfo.dll (Application Information Service) is a Dynamic Link Library (DLL) file related to the key system files of the Windows operating system. Most of it contains a set of basic procedures and driver functions that can subsequently be used in the OS. It can be called one of the most important components in ensuring the correct operation of all programs and applications in the operating system. It must be present on your device, otherwise you will not be able to organize the correct operation of the associated software. That is, Appinfo.dll is part of the Windows Application Information Service, which has a direct relationship with UAC processing.
This library takes full control of the interaction process between UIPI (User Interface Privilege Isolation), performs manipulations with tokens, and also determines the need to launch a particular application on behalf of a regular user or an administrator with elevated access rights. That is, every time users or a separate application launches an interaction process that cannot be implemented without administrator rights, appinfo.dll will check such a request, and then determine whether to grant the appropriate access rights or not.
The most obvious function here will be to launch the consent.exe option, which displays the classic UAC window to request confirmation for escalating privileges within a certain workflow.
Instructions for escalating Local Administrator Protection privileges
The entire process of escalating privileges using Local Administrator Protection involves the implementation of a number of sequential stages:
- Initiation and verification of the registry. As soon as the system receives a request to initialize actions that involve connecting elevated access rights, the Appinfo.dll library will perform a registry check. Here it will look for the TypeOfAdminApprovalMode key. If you currently have Admin Approval Mode enabled, which involves protecting the administrative account, Appinfo.dll will automatically conclude that this request must be processed using not the standard administrator approval mode, but directly using the System Managed Admin Account. This launches the corresponding algorithm.
- Starting Consent.exe. After the system has checked its registry and is sure that the action is correct, the Consent.exe function is launched, which involves processing the request to increase administrative access rights. Among other things, Consent.exe will connect to the SAM database, read the Forward Link SID file from it in the main administrator's record, and then check it in the System Managed Admin Account using the Back Link SID parameter. At this stage, a secure connection is already formed between the main administrator and the account of the system administrator whose access rights allow the upcoming task to be performed. In this case, all operations to increase rights will take place in a completely isolated profile of an additional local system administrator account.
- Switching to the System Managed Admin Account content. As soon as the system is sure that all the work performed at the previous stage was done correctly, Appinfo.dll will automatically switch the active session directly to the System Managed Admin Account context. In this case, the UAC window will use the Admin Approval Mode in its work. There will already be special indicators with a visual component, in particular, there will already be the headings “Windows Security” and the corresponding color scheme displaying the system operation in an isolated context.
- Starting the task in safe mode. At this stage, the workflow is already directly launched, but already under the system administrator account. Due to this, the workflow is isolated from the context of the main administrator, that is, the actions will be performed in a closed local environment.
- Checking the connection security through the SAM database. This is the last stage in the implementation of elevated privileges through the Local Administrator Protection function. Throughout the process that we described above, that is, during the increase in the level of authority, the operating system will periodically return to the Forward Link SID and Back Link SID records, constantly making sure that the legitimacy of the request remains relevant. Thanks to this, hackers will not be able to pass off the fraudulent processes they launched as the local system administrator account, which in itself will provide fairly good security indicators. All this is implemented by creating a strict isolation environment for each individual local account and the corresponding privileges.
That is, Local Administrator Protection — This is a truly advanced tool in providing high security indicators when working in local networks and one of the most advanced innovations in the updated Windows 11 operating system. This is ensured by creating a secure local environment and competent distribution of privileges.
Summing up
Many experts who were engaged in a deeper and more comprehensive analysis of this issue came to the conclusion that the integration of Local Administrator Protection into the general concept of System Managed Admin Account is quite a serious change and a promising contribution to the process of managing the rights of local administrators in general. Thanks to this, Microsoft developers managed to eliminate a lot of classic UAC vulnerabilities that were relevant until relatively recently. Now those tasks, the implementation of which requires access rights with increased privileges, are separated from the basic context of an ordinary user who solves the same type of standard tasks every day.
That is, Local Administrator Protection is what will ensure the most secure and stable work of local administrators. And this solution also sets completely new standards in the field of information security as such and transforms local administrative privileges into a carefully protected resource, excluding their constant exposure to increased risk.
For those who would like to ensure high security indicators, anonymity of work on the network, we recommend paying attention to such a product as mobile proxies from the MobileProxy.Space service. Also, with their help, you can bypass any regional restrictions, access blocking, engage in multi-accounting, web scraping, use many other automated solutions to optimize work processes without the risk of getting banned by the system. That is, your work on the Internet will be as functional, convenient, stable and protected from various hacker influences as possible. You can implement these mobile proxies directly into the Windows 11 operating system, spending a minimum of time and effort on this work.
Follow the link https://mobileproxy.space/en/chto-takoe-mobile-proxy.html to get to know this product in more detail, evaluate its wide functionality, affordable rates. You can also use free testing for 2 hours to finally make sure that such a purchase is worth it. If you have any difficulties in your subsequent work, you will need the help of specialists, the 24-hour technical support service is always in touch.